Toronto Police arrest three behind 'SMS blasters'. Phones lost 911 access for seconds at a time.
Project Lighthouse logged 13 million cellular disruptions from car-mounted IMSI catchers spoofing legitimate towers. Three men face 44 charges in Canada's first SMS-blaster bust.
Toronto Police arrested three people on April 23 in Canada’s first SMS-blaster prosecution, Project Lighthouse. Investigators recorded 13 million cellular network disruptions and infiltrated tens of thousands of devices over the course of the operation. The three suspects face 44 charges combined.
What an SMS blaster actually is
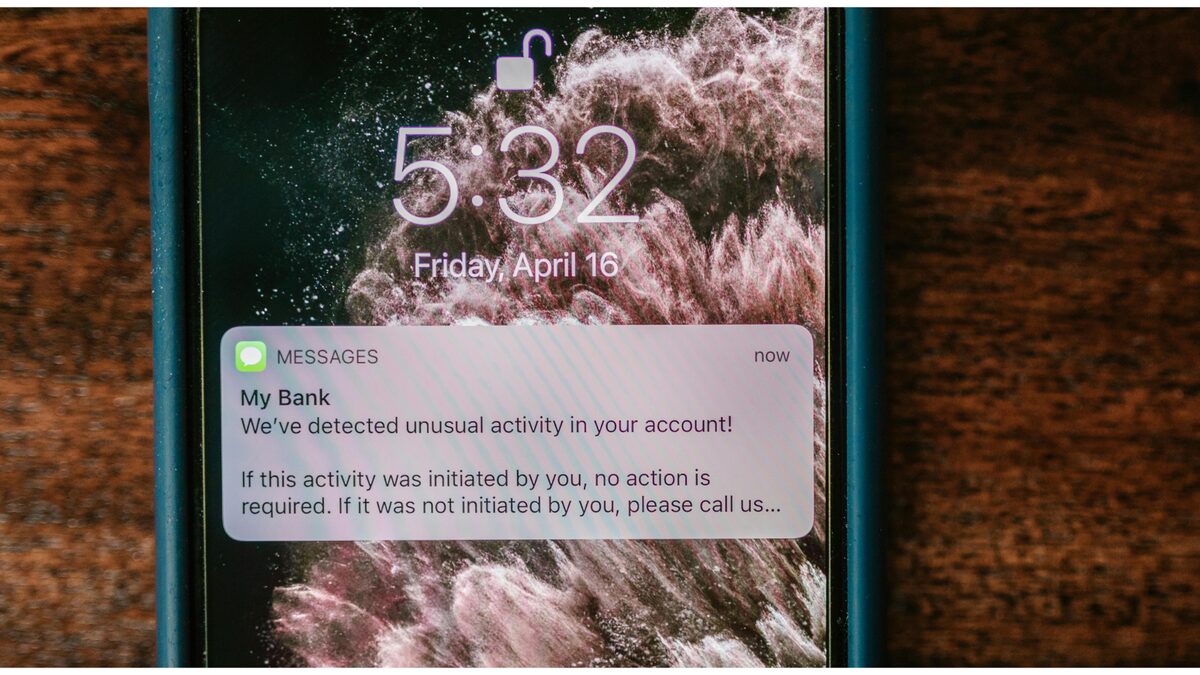
An SMS blaster is a portable IMSI catcher that pretends to be a cell tower. Phones in range connect to it instead of the real network, and the blaster pushes whatever SMS the operator wants directly into the phone’s inbox. Because the blaster bypasses the carrier’s messaging path entirely, it sidesteps every spam filter and sender-reputation check the carrier has built up.
The Toronto suspects ran the blasters out of cars driven around downtown, per Tom’s Hardware’s reporting. When a target phone connected to the fake tower, two things happened. First, it received a fraudulent text spoofing a bank or delivery company. Second, while it was attached to the rogue tower, the phone couldn’t make outbound calls on the legitimate network, including emergency 911 calls. Toronto Police logged blocks ranging from seconds to several minutes per device.
What we know
Pull from the Toronto Police Service press release:
- Investigation start: November 2025, after a security partner alerted police to a suspected blaster operating in downtown Toronto.
- Suspects: Three men, charged with 44 offenses combined, including possession of devices used for cybercrime, defrauding the public, and possession of stolen property.
- Hardware: Multiple SMS-blaster appliances seized, plus vehicles used to drive them through dense urban areas.
- Scope: 13 million network disruptions recorded. Tens of thousands of phones connected to the rogue towers at some point during the operation.
- Partners: RCMP National Cybercrime Coordination Centre (NC3), York Regional Police, Hamilton Police Service, major Canadian banks, and Canadian telcos.
Deputy Chief Robert Johnson framed the public-safety angle directly: “It had the ability to reach thousands of devices at once. And beyond the financial risk, there are real public safety implications. For instance, when devices are diverted from legitimate networks, even briefly, it interferes with a person’s ability to connect to emergency services.”
What we don’t know
Two things stand out. First, who built the hardware. SMS blasters in this format are commercial product, available on grey-market channels mostly out of Southeast Asia. Toronto Police haven’t disclosed the make or whether the suspects bought a turnkey kit or assembled one. That detail matters because it tells you whether other operators in Canada have access to the same equipment.
Second, who got hit. The TPS hasn’t named which banks were impersonated in the smishing texts, and hasn’t said how many of the tens of thousands of contacted devices actually had credentials stolen versus just received a phishing SMS. The 13 million figure is disruptions, not victims. The victim count is going to be smaller, and we don’t have it yet.
How this fits the broader pattern
SMS-blaster busts have been climbing internationally for the past 18 months. The UK Met Police arrested operators in London in late 2024. Thai authorities seized vehicle-mounted blasters in Bangkok last summer. Vietnamese police hit a similar operation in Ho Chi Minh City. The Canadian case is the first in North America at the press-release level, and the scale (13 million disruptions in one urban metro) is an order of magnitude above most prior arrests.
What makes the format hard to defend against is that nothing on the user side flags it. Your phone shows full bars, the SMS arrives looking like it came from your bank’s short code (the From line spoofs whatever the operator types), and the tower-attach handshake doesn’t surface to the user. The defense is in the network: carriers can detect rogue base stations through signal-pattern analysis, and 5G’s mutual authentication closes the IMSI-catcher hole entirely on devices that have a 5G-only mode available. But Canadian and U.S. networks still fall back to 4G and even 3G regularly, and that’s the window the blasters exploit.
What this means for you
If you live or work in a dense urban area, the practical defenses are limited but real.
Lock your phone to 5G-only if your device exposes the toggle. iOS doesn’t surface this directly, but enterprise MDM profiles can; Android offers it under “preferred network type” on most builds. 5G mutual authentication makes IMSI catching meaningfully harder, and if the rogue tower can only push 4G, your phone won’t attach to it.
Don’t trust SMS for anything that matters. Banks, delivery companies, and government agencies all know this; the ones still using SMS for second factors are doing it because their fraud team accepted the risk. If you’re getting a text asking you to “verify” something, open the actual app instead. The whole point of an SMS blaster is that the From line tells you nothing.
If you’re a security engineer at a Canadian bank or telco, the TPS press release lists the partner agencies you can route IOCs through. The blasters were hardware. Hardware leaves a procurement trail. The next bust is going to come from somebody following that trail backward, and it’s worth knowing who at the RCMP NC3 to call.
The piece that should make your security review change today: this is the same vector behind the Vercel breach earlier this month and the npm supply-chain LLM proxy we covered last week. None of these attacks are technically novel. What’s novel is the operational scale at which low-cost commodity hardware lets a three-person crew run a fraud operation that would have required a nation-state in 2018. The threat model has flattened. Plan for that.
Share this article

Sources
- Mobile SMS blasters in vehicles prowled Canadian streets, causing 13 million network disruptions — Tom's Hardware
- Arrests Made in Project Lighthouse, First-of-its-Kind SMS Blaster Investigation in Canada — Toronto Police Service
- Unprecedented SMS Blaster Arrests — Toronto Police Service
- Toronto police seize first SMS blasters in Canadian cybercrime probe — Toronto Today